The debate around DPDPA vs GDPR architecture is growing across Indian boardrooms. Many enterprises assume that GDPR-ready systems automatically meet DPDPA requirements. However, this assumption can create serious compliance risk.
While both laws protect personal data, their architectural expectations differ significantly. Under the DPDP Rules 2025, compliance is no longer documentation-heavy. It is infrastructure-heavy.
Therefore, Indian enterprises must evaluate whether their current systems truly align with DPDPA’s technical mandates.
DPDPA vs GDPR Architecture: The Structural Difference
GDPR is principle-driven. It emphasizes accountability, consent, and data minimization.
In contrast, DPDPA introduces enforceable technical safeguards under:
Rule 6(1)(a): Encryption, masking, and virtual tokens
Rule 6(1)(g): Technical and organisational measures
Rule 8(3): Data erasure
Rule 13(3): Audit and traceability
As a result, DPDPA vs GDPR architecture comparison reveals a critical shift. DPDPA focuses on reducing exposure, not just regulating access.
Why GDPR-Based Architectures Fall Short in India
Many Indian enterprises implemented GDPR-inspired controls such as:
- Database encryption
- Role-based access control
- Consent dashboards
- Log aggregation systems
- However, these controls still allow applications to access raw PII.
- This creates exposure during:
- Insider misuse
- Application-level vulnerabilities
- Lateral attacker movement
- Database breaches
- Consequently, even encrypted systems may fail under DPDPA if raw PII becomes accessible during processing.
What DPDPA Requires at the Technical Level
The core of DPDPA vs GDPR architecture differences lies in exposure management.
Under DPDPA, enterprises must:
- Isolate PII in a secure Data Privacy Vault
- Replace sensitive fields with virtual tokens
- Enable searchable encryption without decryption
- Maintain centralized, immutable audit trails
In addition, erasure workflows must propagate cleanly across systems.
This is not a patch. It is an architectural redesign.
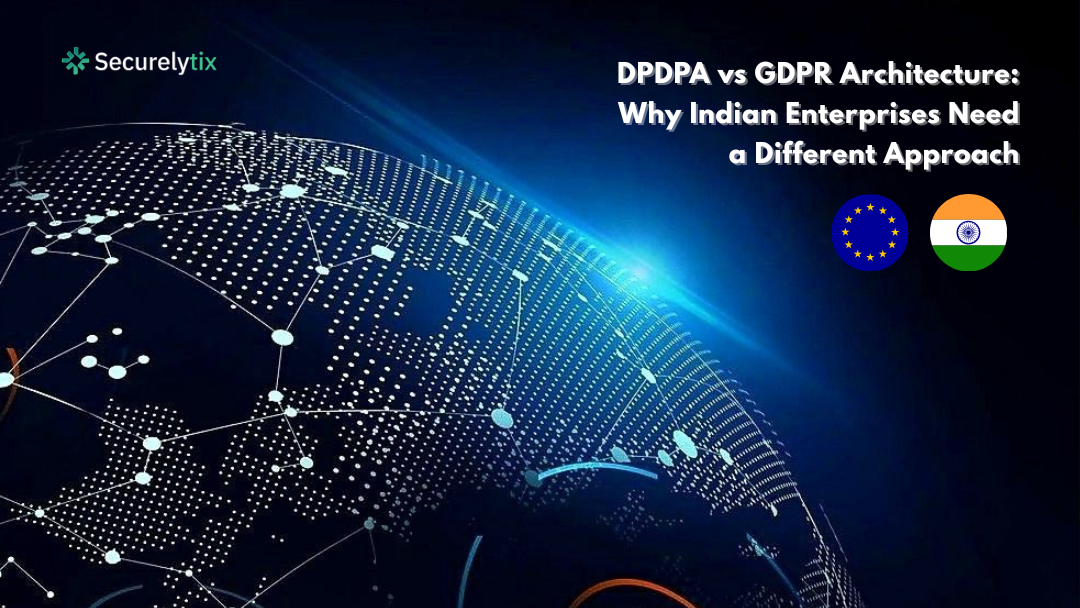
The Role of a Data Privacy Vault in DPDPA Compliance
A Data Privacy Vault stores real PII in a hardened environment and replaces it with tokens across business systems.
Therefore:
- Applications process tokens instead of raw personal data
- Breach impact is dramatically reduced
- Audit scope becomes centralized
- Consent withdrawal and erasure become operationally simpler
This vault-based model is what differentiates DPDPA-ready architecture from traditional GDPR-based designs.
Comparison: GDPR vs DPDPA-Ready Architecture
| Feature | GDPR-Inspired Model | DPDPA-Ready Architecture |
| Data Storage | Encrypted DB with app access | PII isolated in Data Privacy Vault |
| Search | Decrypt during query | Searchable encryption |
| Usage | Apps access raw PII | Apps use virtual tokens |
| Audit | Distributed logs | Centralized immutable audit trails |
| Breach Impact | High exposure | Minimal usable data |
Ultimately, the DPDPA vs GDPR architecture gap becomes clear at the processing layer.
Frequently Asked Questions on DPDPA vs GDPR Architecture
Is DPDPA stricter than GDPR?
DPDPA is not broader. However, it is technically explicit and penalty-driven. Financial penalties can reach ₹250 Crores.
Is encryption alone enough under DPDPA?
No. Encryption at rest and in transit is necessary but insufficient. If PII is decrypted during processing, exposure risk remains.
Why is tokenization important in DPDPA architecture?
Tokenization ensures that business systems operate on non-sensitive substitutes. This reduces breach impact and simplifies compliance under Rule 8 and Rule 13.
Why Indian Enterprises Need a Different Architecture
India’s digital ecosystem is high-volume and identity-rich. As a result, exposure risk is amplified.
Enterprises that continue relying on perimeter-focused GDPR controls may struggle under DPDPA audits.
In contrast, vault-based systems:
Shrink compliance surface area
Reduce breach blast radius
Simplify audit traceability
Enable zero-exposure processing
Securelytix enables this shift by providing a PII Data Vault designed specifically for DPDPA Rule 6 safeguards.
Conclusion: Compliance Is Architectural
The conversation is no longer simply about DPDPA vs GDPR as laws. It is about DPDPA vs GDPR architecture.
Does your system minimize exposure? Or does it only encrypt risk?
Indian enterprises that adopt vault-based architecture early will not just comply. They will de-risk their entire data ecosystem.
#DPDPA #DPDPRules2025 #GDPR #GDPRCompliance #DataPrivacy #DataProtection #PIISecurity #DataVault #SearchableEncryption #EnterpriseSecurity #Securelytix