Securing PII in AI Pipelines: How to Feed LLMs Enterprise Data Without Leaking Customer Information.
Every enterprise AI project eventually hits the same problem: the data that makes an LLM genuinely useful (real...
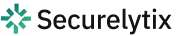
How to Build a Zero-Trust Data Access Layer: Architecture Patterns for Enterprises Handling Sensitive Customer Data
The most dangerous assumption in enterprise software isn’t a bug in your code. It’s this: if a request...
Why Traditional Encryption Fails Under DPDPA
For decades, encryption has been the standard defense for protecting sensitive data and Personally Identifiable Information (PII). Encrypting...
DPDPA vs GDPR Architecture: Why Indian Enterprises Need a Different Approach.
The debate around DPDPA vs GDPR architecture is growing across Indian boardrooms. Many enterprises assume that GDPR-ready systems...
Understanding Rule 6: The Technical Core of DPDPA Compliance.
With the notification of the DPDP Rules 2025, the standard for data protection in India has shifted from...

Securing PII at All Times: What DPDPA Really Demands from Indian Enterprises
With the notification of the Digital Personal Data Protection (DPDP) Act, the landscape for handling personal data in...
You may also like