With the notification of the DPDP Rules 2025, the standard for data protection in India has shifted from general “best practices” to specific technical mandates. For enterprises handling personal data, Rule 6 is the most critical section to understand, as it defines the “reasonable security safeguards” required to prevent data breaches and the catastrophic penalties – up to ₹250 Crore – that follow them.
Compliance now requires a dual approach: sophisticated technical tools and robust organizational frameworks.
1. Rule 6(1)(a): Technical Safeguards (Encryption & Tokenization)
Rule 6(1)(a) explicitly mandates the use of encryption, obfuscation, masking, and virtual tokens mapped to personal data. However, the real-world challenge for a B2B enterprise is maintaining business utility while ensuring security.
- The Limitation of Standard Encryption: Traditional encryption protects data “at rest” (on a disk), but the data is often exposed the moment a user searches for a record or a system processes a transaction.
- The Power of Virtual Tokens: This is the most effective safeguard mentioned in Rule 6. By replacing PII (Personally Identifiable Information) with a virtual token, the sensitive data is isolated. Your internal systems process the token, which looks like the real data but holds no value for an attacker.
- Searchable Encryption: To remain compliant while staying operational, enterprises are moving toward searchable encryption for PII. This allows you to query a database (e.g., finding a customer by their phone number) without ever decrypting the data, ensuring the PII is never “exposed” during the search process.
2. Rule 6(1)(g): Organisational Measures (Effective Observance)
Technical tools are ineffective without an enforcement layer. Rule 6(1)(g) focuses on “effective observance,” requiring enterprises to implement “appropriate technical and organisational measures” to ensure safeguards are actually followed.
This involves:
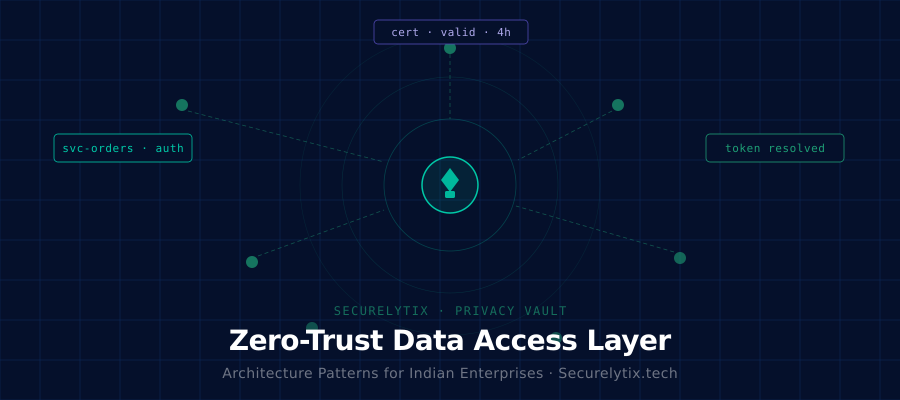
- Access Governance: Moving beyond simple passwords to “Zero Trust” architectures where access to decrypted PII is restricted by role, time, and necessity.
- Continuous Audit Trails: Maintaining detailed logs of who accessed what data and when. Under DPDPA, these logs are vital for proving “effective observance” during a regulatory audit.
- Data Minimization: Ensuring that only the specific data required for a task is accessible, often achieved through dynamic masking.
Comparison: Traditional Security vs. Rule 6 Compliant Architecture
| Feature | Traditional Security | DPDPA Rule 6 Standards |
| Data Storage | PII stored in plain text or standard DB encryption. | PII isolated in a Data Privacy Vault. |
| Search Method | Decrypting data to perform a search. | Searchable Encryption (No exposure). |
| Data Usage | Applications touch raw PII directly. | Applications use Virtual Tokens. |
| Auditability | Scrambled logs across various servers. | Centralized, immutable Audit Trails. |
Relevant Q&A: Navigating the New Compliance Standard
Q: Is standard SSL/TLS (Encryption in Transit) enough to satisfy Rule 6?
A: No. While TLS is necessary, Rule 6 focuses on the data itself. You must protect the data while it sits in your database and while it is being used by your applications. If a database breach reveals plain-text PII, having TLS for your website will not prevent a penalty.
Q: How do “Virtual Tokens” help with data erasure requests (Rule 8)?
A: When a user exercises their right to be forgotten, deleting a single record in a central Vault is much simpler than hunting for that user’s PII across 50 different backup tapes and microservices. The “Tokens” in those systems simply become orphaned and useless.
Q: What qualifies as “Effective Observance” under 6(1)(g)?
A: It means having a verifiable system in place. If an auditor asks how you prevent a support executive from downloading your entire customer list, you must show technical blocks (like rate limiting and masking) and organizational logs that prove those blocks are working.
The Path Forward: Zero-Exposure Architecture
For Indian enterprises, the goal is no longer just “security”- it is de-risking. By adopting a Data Privacy Vault approach, businesses can decouple identity from utility. When you replace raw PII with virtual tokens and utilize searchable encryption, you significantly shrink your compliance surface area.
Implementing these Rule 6 safeguards ensures that even if your primary application environment is compromised, the sensitive personal data remains encrypted, tokenized, and mathematically beyond the reach of unauthorized parties.
If your organisation is preparing for DPDP compliance and wants to reduce PII risk without breaking operations, Securelytix is your trusted partner for privacy-by-design security at scale.
Book a demo right now to strengthen your Data Security Posture Management with Securelytix. Thanks.
#DPDPA #DPDP #DPDPRules2025 #DataProtection #DataPrivacy #DataSecurity #PII #PIISecurity #PIIProtection #PIIDataVault #DataPrivacyVault #Tokenization #VirtualTokens #Securelytix